If there’s one thing the pandemic has taught us, it’s that many traditional workplace norms and rules don’t apply anymore. We don’t need physical office spaces, business casual dress codes, or a five-day, 40-hour workweek.
It used to be standard practice to equip employees with company laptops or smartphones. Now, more businesses allow employees to use their personal devices for work purposes. Having a Bring Your Own Device (BYOD) arrangement has many pros and cons. Specifically, when your company doesn’t own the devices your teammates use, it can make it harder for you to control how they use them and keep company information secure. Your team may also have concerns about how much access your company will have to their BYOD devices and personal data.
A BYOD policy can provide much-needed clarity and set clear terms and expectations around device security, company access, reimbursement, risk and liability, employment termination, and policy violations. In this article, we’ll go over what you should include in your BYOD policy, the overall benefits of having one, useful software solutions for implementing and enforcing a BYOD policy, and offboarding recommendations for BYOD companies. Plus, we’ll share a template you can use as a springboard if you’re looking to launch a BYOD policy within your organization.
What to include in your BYOD policy
Before you start drafting, Steph Little, a senior HR consultant and policy and compliance lead at Bright + Early, recommends founders take a step back and consider the following questions:
- What are you trying to solve/prevent/encourage/convey with this policy?
- What actions do you need to take to do that?
Check out our BYOD policy template so you can follow along in the next section of this guide.
Keep in mind while this BYOD policy template can serve as a starting point for your team, the terms and exact requirements may vary. For example, your team may need to adhere to specific security compliance standards based on your industry. Even if you work with an HR consultant to create a BYOD program, be sure to consult with a lawyer before rolling out any BYOD policy.
What makes up a documented BYOD policy?
A BYOD policy should address all the potential concerns that an employer, and their employees, may have about using personal cell phones or laptops for work. For example, most BYOD policies address the following matters:
- Privacy Expectations: From the outset, it should be clear that employees will have no expectation of privacy in any company content stored, received, transmitted, or created on any applicable device. To that end, your organization should explicitly articulate that it reserves the right to monitor, review, intercept, and remotely wipe applicable content on a device, in its sole discretion.
- Acceptable use policy: What activities are explicitly prohibited? What company resources are explicitly allowed to be accessed using a mobile device? For example, some policies prohibit employees from accessing unsecured sites or using personal social media applications during work hours.
- Devices and IT support: What types of devices can employees use? What are your company’s IT/software requirements? What happens if your employees have IT issues? What if their device requires upgrades? Some policies prohibit employees from using rooted (Android) or jailbroken (iOS) devices.
- Reimbursement: Will the company cover any costs associated with devices? For example, will the company pay for a portion of an employee’s smartphone bill, reimburse expenses, or provide a monthly stipend?
- Security measures: What security requirements will you have to allow for the safe use of personal devices (e.g., anti-virus software, malware protection, multi-factor authentication, strong passwords)? How do you intend to protect your employees’ safety?
- Risks/Liabilities/Disclaimers: What happens if the device needs to be wiped or disabled? What happens in the case of loss or theft? Who is liable for risks or costs? Some companies require their employees to install “remote-wipe” software so company-related data can be erased remotely.
- Confidentiality and Proprietary Rights: Employees should be reminded that misuse of their own devices could adversely impact your organization’s ability to safeguard its confidential and proprietary information. Unauthorized disclosure of such information should be strictly prohibited. If you have a separate confidentiality/proprietary rights agreement or policy, consider also referencing such document in this section.
- Violations of policy: What happens if the employer or employee violates the policy? In other words, will your company take any disciplinary action or terminate an employment contract?
- Termination of employment: What happens to the device when you terminate an employee? Some companies ask terminated employees to present the personal device for inspection or remotely wipe the device.
- Work-life balance: When do you expect employees to respond to work-related communications, including emails, telephone calls, video calls, and other messages? Do employees need to turn on out-of-office notifications or change their voicemails when they are not scheduled to work? Your employees have a right to disconnect, and some countries are even creating policies about this.
- Employee Acknowledgement: As with all employee handbooks and standalone policies, your BYOD policy should conclude with an acknowledgment by the employee that they have received, read, and understand the policy. Importantly, they should acknowledge that the BYOD policy will not change their at-will employment status.
Remember again to cover your bases and make sure you vet any policy with a legal professional before implementing.
Steph also suggests founders review their draft with the following questions in mind:
- Is this policy in line with our current or aspirational values?
- Could this policy cause the company or our employees harm?
- Who specifically does this policy serve? Who does it exclude or impact negatively?
- How can we mitigate negative impact? What fair exceptions would we make?
- Will this policy still work when we are double, triple, or 10X our size? (It’s OK if the answer to this one is no. You can revise your policy as you grow.)
After you review and redraft, make sure to:
- Seek and incorporate appropriate feedback.
- Get your legal department or counsel to review the policy and ensure it complies with applicable laws (particularly local employment and privacy laws).
- Share the policy with your team. Ensure your employees understand it and have the opportunity to ask questions.
- Educate new hires on your BYOD policy by incorporating it into your employee handbook and onboarding materials.
- Finally, regularly review and update your policy as needed.
7 useful solutions for implementing a BYOD policy
Nowadays, there’s an app for everything, and BYOD implementation is no exception. Although device management, security, and compliance can be a little more complicated with personal devices than company tech, there are plenty of solutions designed to make this process a lot easier and more efficient. Here are a few of our favorite tools.
1. Rippling for device management
Device management solutions like Rippling allow employers to effortlessly manage employee apps, devices, data, and security – 100% remotely – in one unified system. For example, Rippling can give your HR or IT teams the power to fully set up employees’ computers and apps in just 90 seconds and deploy BYOD security best practices across your apps and devices in minutes. It covers everything from app and identity management to device and inventory management and can help you seamlessly and securely onboard and offboard your employees.
2. LastPass for password management

Tired of changing passwords every time an employee leaves? Worried a terminated employee might still have access to company apps or data? With LastPass, you can eliminate employee password reuse with their integrated Password Generator, manage passwords from one place, protect sensitive data with their zero-knowledge security model, and share passwords simply and safely.
3. Okta for Single Sign-On (SSO)
With SSO, your employees can use one set of login credentials – for example, a name and password – to access multiple applications. Unfortunately, while SSO can be convenient for your team, it can also open you to security risks. For example, a hacker who gains control over a user’s SSO credentials could access every application the user has rights to.
A solution like Okta can help your employees log in to work apps faster without sacrificing security. The SSO provider has a network of 7,000+ pre-built integrations that can help you securely adopt and deploy SSO to cloud apps in weeks, not months, all without building and maintaining the integrations yourself. It also has built-in cybersecurity tools like Okta Insights to identify and block malicious login attempts automatically.
4. Vanta for compliance
Vanta helps companies achieve SOC 2, ISO 27001, HIPAA, PCI, and GDPR compliance by automating their security monitoring, getting them security audit-ready in weeks instead of months. All you need to do is connect your tools to Vanta, fix the gaps on your dashboard, and then work with a Vanta-trained auditor to complete your audit. The auditor will guide you throughout the process and help tailor your security monitoring and compliance to meet your business and customers’ needs.
5. Notion for team wiki
Once you finalize your BYOD policy, you need an accessible and secure place to store it – that’s not just a floating Google Doc in your team drive.
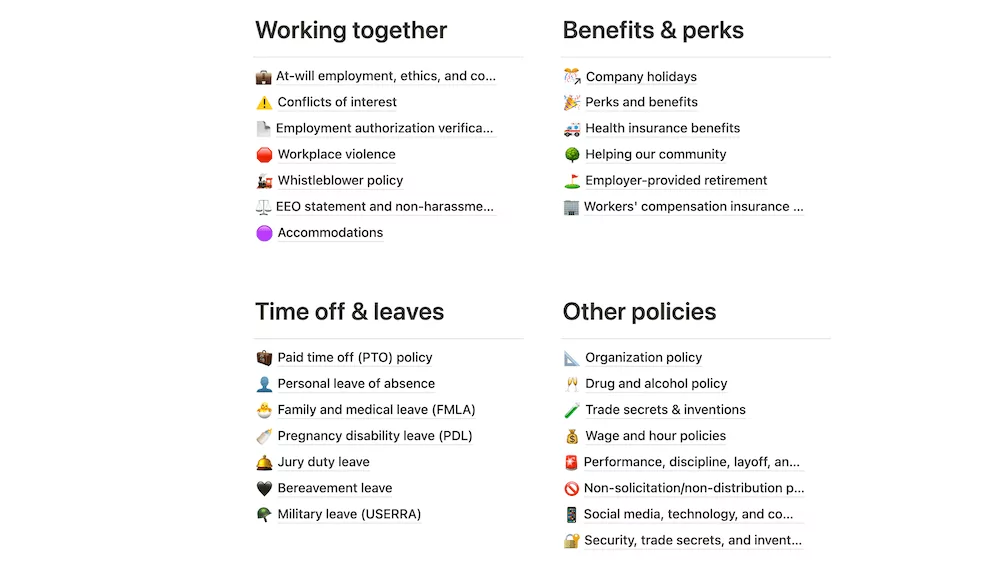
We use Notion to store and share all of our HR and IT policies.
6. NordVPN for Virtual Private Network (VPN)

When your employees only work at the office, you at least have the peace of mind of knowing they’re accessing corporate data and files on a secure company network. However, if they work outside the office and use public WiFi connections, this can be a significant security risk and could make your company vulnerable to cyberattacks.
NordVPN is a VPN service that can protect your employees’ internet connection and privacy online by creating an encrypted tunnel for their data and hiding their IP addresses. It can be handy if your employees are traveling and need to access home content or if they regularly use public WiFi.
7. OpenPhone for business phone solution
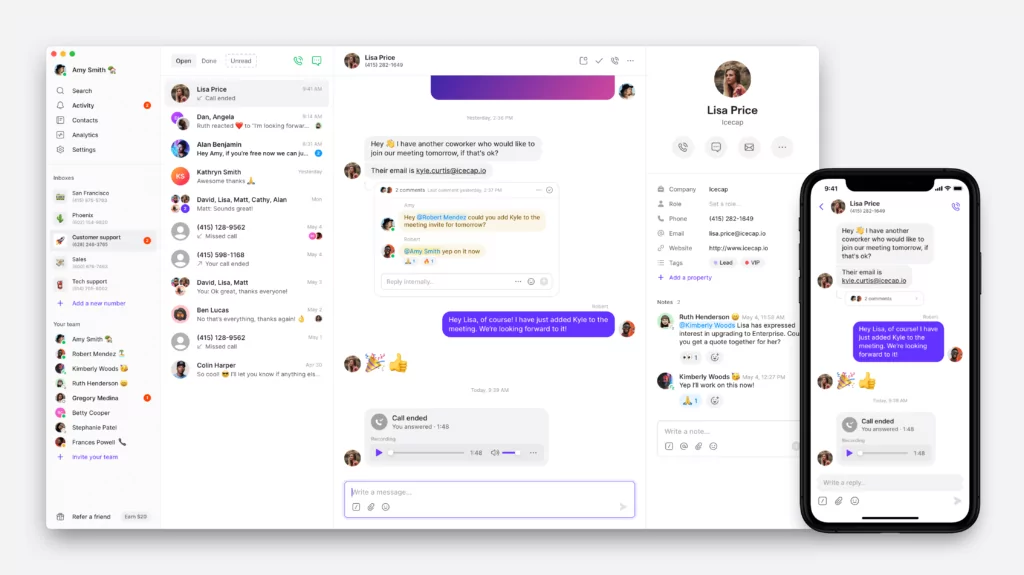
Last but certainly not least, there are business phone solutions. VoIP providers like OpenPhone allow employees to add work phone numbers to their existing devices – essentially turning their personal devices into a company phone.
OpenPhone helps your employees have a better work-life balance and protect their information by keeping work and personal communications separate, even when they’re using a personal device.
Plus, with OpenPhone, your employees can use their US, Canadian, or toll-free number on any device with an internet connection and set up business hours to mute work calls and messages when they’re off the clock.
How to offboard teammates when you have a BYOD policy
BYOD programs may eliminate the hassle of tracking down and collecting hardware when an employee leaves. However, it can also make your company more vulnerable to severe breaches if the terminated employee has ill feelings about their termination. Their personal devices contain sensitive information, and since you can’t retrieve them, you need to take swift measures to protect your company’s data.
Here are some BYOD offboarding best practices:
- Terminate personal device access. Require them to remove any work-related data, programs, or apps immediately from their devices before leaving. Even if your employee departs on good terms, they could still walk away with proprietary data, or a hacker could gain access to your system and files using stolen credentials.
- Revoke network access. Eliminate the employee’s unique identity and revoke their access to company applications and third-party cloud-based programs. Also, change any common passwords for these applications or other system tools.
- Remove employee data from systems. Ensure terminated employees don’t show up on contact lists, in meeting rosters, or as the primary contacts for projects. You should also have all communications from terminated employee accounts forwarded to a manager or supervisor.
- Follow a set procedure. A standard checklist of offboarding best practices ensures you don’t miss any critical actions and reduces the risk of disgruntled employees making things difficult after leaving. If you need inspiration, you can check out our offboarding checklist here.
- Document your offboarding actions. This step is necessary for compliance in some industries, especially in cases where terminated employees could potentially take or publicly distribute sensitive information.
Why growing teams have a clear BYOD policy
Creating formal guidelines and policies can feel like a hassle or overly bureaucratic when you’re just starting up. For example, when you have less than ten employees, you might have more of a “go with the flow” approach to policies – addressing issues when they arise rather than trying to predict every possible dilemma.
“Most of the startups we work with don’t create a BYOD policy until something happens,” says Steph. “It will typically come into play the first time a key new hire says something is a dealbreaker or when we run into a technical or safety issue.”
However, if a co-founder or someone else on your team is still on the fence about having a policy, here are three critical reasons why you should be more proactive and set up a clearly documented BYOD policy early:
1. Prevent worst-case scenarios
As your company grows, a BYOD arrangement can quickly hurt more than it helps without a clear policy. For example, maybe your company has experienced data breaches. Or you lose out on a star candidate because they can’t afford the upfront costs of a new device or data plan. Or maybe you’ve found out that a terminated employee has stolen company data.
Without a BYOD policy, the consequences of these worst-case scenarios could be expensive at best and disastrous at worst.
“Credit card information that even a small online store collects is valuable to a hacker, and SMBs systems are generally easier to break into than larger companies. A data breach like this can cost a company an average of $100,000,” says Amy Van Es, tech ethicist and founder of Memo, an organization on a mission to help people and organizations to become good digital citizens.
2. Set clear expectations from the beginning
There are also the everyday hassles of not having clear guidelines in place. For instance, what happens to the devices when an employee leaves? Or if an employee’s device is lost, stolen, or needs upgrading? What if an employee goes over their monthly data plan because of work? A BYOD policy will help ensure you and your employees are on the same page and avoid mismatched expectations.
For example, Lisa Isaac, Founder of Lisa Isaac HR, has a BYOD policy for her small business and includes the terms in her employment contract. “When people are offered a job, it’s written right into the contract that they’re expected to use their own devices and internet unless they come to the office,” she says.
3. BYOD is more complex than you think
BYOD policies are not solely an HR, legal, or IT department issue. It involves all of these different areas and it can take time to develop a comprehensive policy that works for all of these departments. You also have to think about your employees. You need to keep their safety and financial situation in mind and respect that the device ultimately belongs to them. It’s a complex issue, and it can take time to consider all of these perspectives, so it’s better to start this work early.
Going with the flow only works for so long
Allowing your employees to use their personal devices for work may seem simple at first. But without a proper strategy and policy in place, you could be opening a pandora’s box of serious privacy, security, and DEI issues. But if you follow the best practices above, you’ll be well on your way to creating a policy that protects your people and your organization. If you’re still weighing whether to implement a BYOD policy, check out our guide to BYOD pros and cons.
